Streamlining Patch Management: Unleashing the Power of AWS Systems Manager Patch Manager
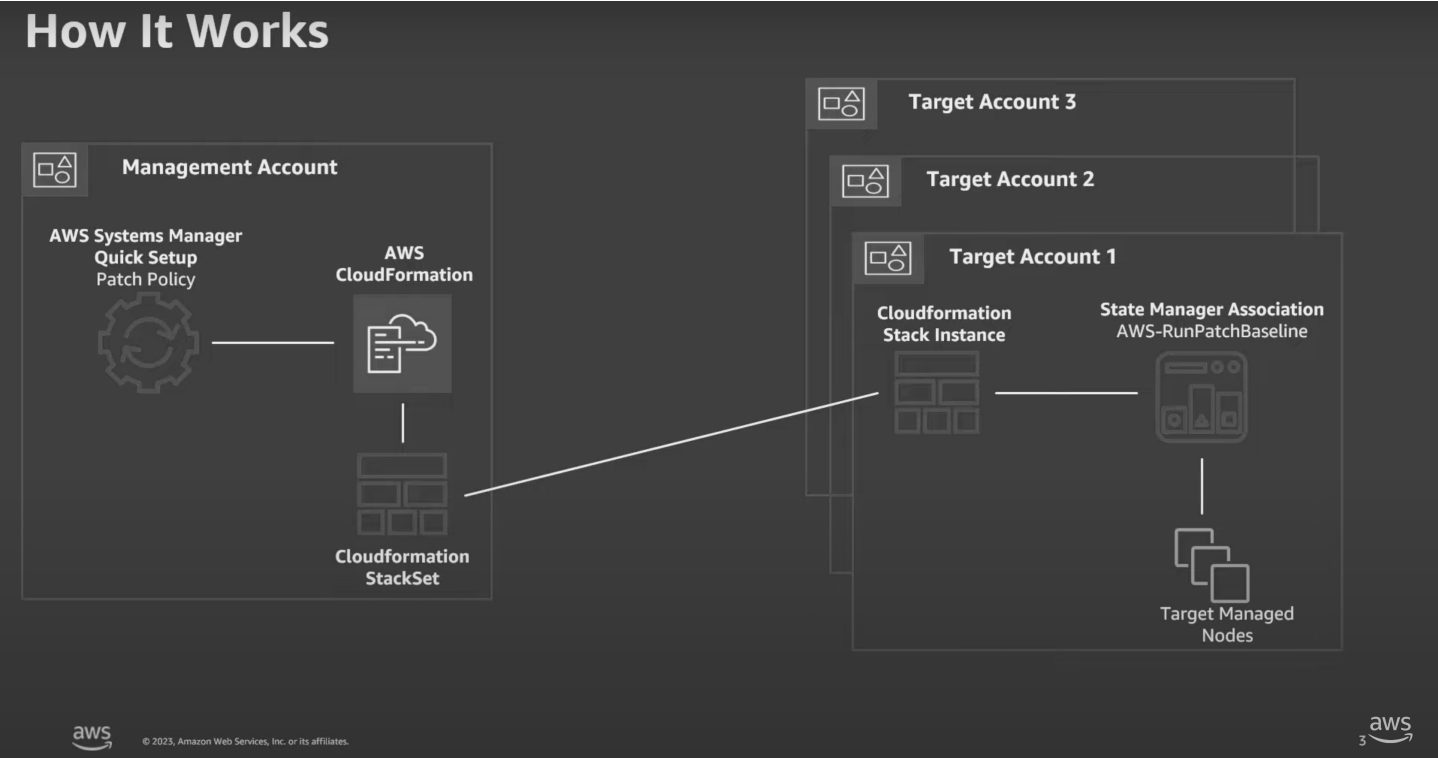
In today’s fast-paced cloud computing environment, the security and integrity of systems are of utmost importance. For businesses utilizing Amazon Web Services (AWS), this means ensuring that software is regularly updated with the latest security patches and updates—a task that is crucial yet complex and time-consuming. AWS Systems Manager Patch Manager presents a streamlined solution to this challenge, enabling AWS Cloud Services partners, such as Aligned Technology Group, to automate the patching process for EC2 instances and on-premises servers efficiently.
Understanding the Essentials of Patch Management:
Patch management plays a pivotal role in enhancing the security posture of systems by applying updates to mitigate vulnerabilities and improve functionality. However, the diversity of operating systems, such as Linux, MacOS, and Windows, and the necessity for manual intervention, make patch management a daunting task. This complexity is compounded when managing patches across various platforms and global networks.
The Role of AWS SSM Patch Manager in Simplifying Patch Management
AWS SSM Patch Manager stands as a formidable solution designed to automate the patching process, supporting a wide range of operating systems. This automation fosters a unified approach to patch management across different environments, significantly easing the administrative workload and reducing the margin for error.
Implementing Effective Patch Baselines
At the heart of Patch Manager’s efficiency are patch baselines, which establish rules for applying patches. These baselines allow for the customization of update approvals or rejections, with a default focus on critical and security-related patches to ensure managed instances are kept secure with minimal manual intervention.
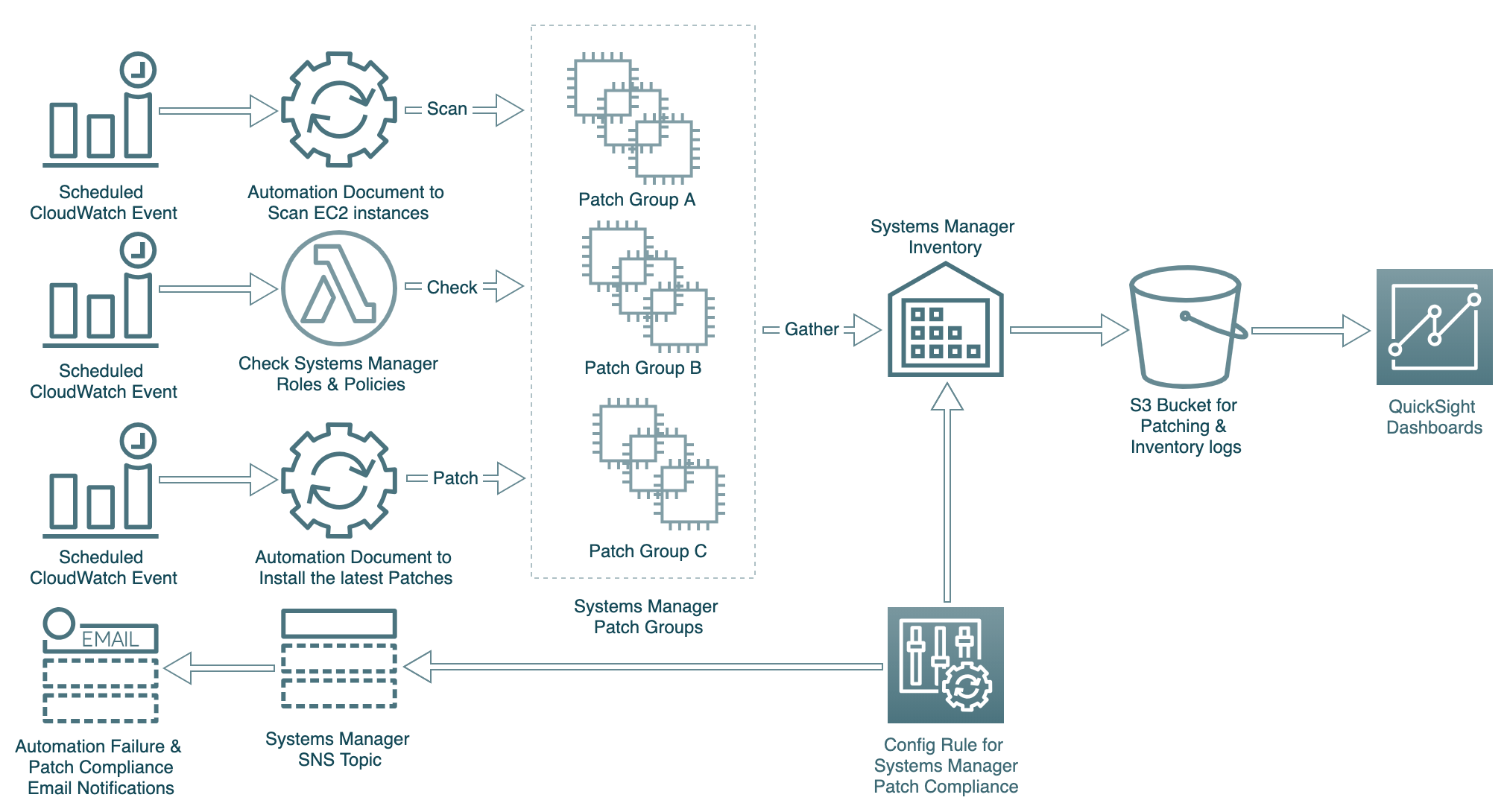
Organizing with Patch Groups
Patch groups offer an additional layer of organization in patch management by linking sets of instances to specific patch baselines. This feature facilitates targeted patching strategies across various environments like development, testing, and production, ensuring updates are applied judiciously.
Flexibility and Customization in Patch Management
Patch Manager provides the flexibility of on-demand or scheduled patching through maintenance windows. After patching, it generates a comprehensive compliance report, detailing the patch status of each instance—a feature that is invaluable for in-depth analysis and record-keeping.
Customization and Control with Patch Manager
For organizations with unique patching needs, Patch Manager allows for the creation of custom patch baselines, offering precise control over the patching process. AWS also provides predefined patch baselines for common operating systems, ensuring instances remain updated effortlessly.
Maximizing Maintenance Windows
Maintenance windows are crucial for implementing patch management strategies effectively, allowing administrators to schedule patching during low-activity periods. This scheduling minimizes the impact on system availability and performance, maintaining system reliability and user experience.
Securing AWS Environments with Patch Manager
AWS SSM Patch Manager is instrumental in automating security patching in AWS environments, ensuring systems remain secure, compliant, and up-to-date. By leveraging Patch Manager, AWS Cloud Services partners like Aligned Technology Group can offer their clients peace of mind, knowing their systems are protected against vulnerabilities and optimized for performance.
Integrations:
Patch Manager integrates with the following other AWS services:
-
AWS Identity and Access Management (IAM) – Use IAM to control which users, groups, and roles have access to Patch Manager operations.
-
AWS CloudTrail – Use CloudTrail to record an auditable history of patching operation events initiated by users, roles, or groups.
-
AWS Security Hub – Patch compliance data from Patch Manager can be sent to AWS Security Hub. Security Hub gives you a comprehensive view of your high-priority security alerts and compliance status. It also monitors the patching status of your fleet.
-
AWS Config – Set up recording in AWS Config to view Amazon EC2 instance management data in the Patch Manager Dashboard.
FAQs
-
What is AWS SSM Patch Manager? AWS SSM Patch Manager is a tool within AWS Systems Manager that automates the process of patching managed instances, including EC2 instances and on-premises servers.
-
Can I customize patch baselines in Patch Manager? Yes, Patch Manager allows you to create custom patch baselines, enabling you to specify which patches are approved or rejected for your instances.
-
What are patch groups in AWS Patch Manager? Patch groups are used to associate a set of instances with a specific patch baseline, facilitating organized and targeted patching across different environments.
-
How does Patch Manager handle compliance reporting? After a patching operation, Patch Manager generates a compliance report detailing the patch status of each instance, which can be sent to S3 for further analysis.
-
Can Patch Manager automate patching during specific times? Yes, Patch Manager can schedule patching during maintenance windows, allowing you to define specific times for patching to minimize impact on system availability.
Strategically Aligning Technology to Business
© 2023 ALIGNED TECHNOLOGY GROUP Terms of Use Online Privacy Notice Cookie Policy
Last Updated on May 1, 2024 by Lauryn Colatuno


